HashiCorp Vault Unveils AI Agent Security: Identity and Authorization for Autonomous Systems
As organizations integrate AI agents into their workflows, traditional IAM models fall short because autonomous, non-deterministic actors require dynamic, context-aware controls. HashiCorp Vault now introduces a dedicated framework for securing AI agents, addressing identity, delegation, runtime policy evaluation, and ephemeral authorization. This Q&A explores the new capabilities such as the agent registry, granular policies, and per-request access controls.
1. Why does AI agent security demand a fundamentally new authorization model?
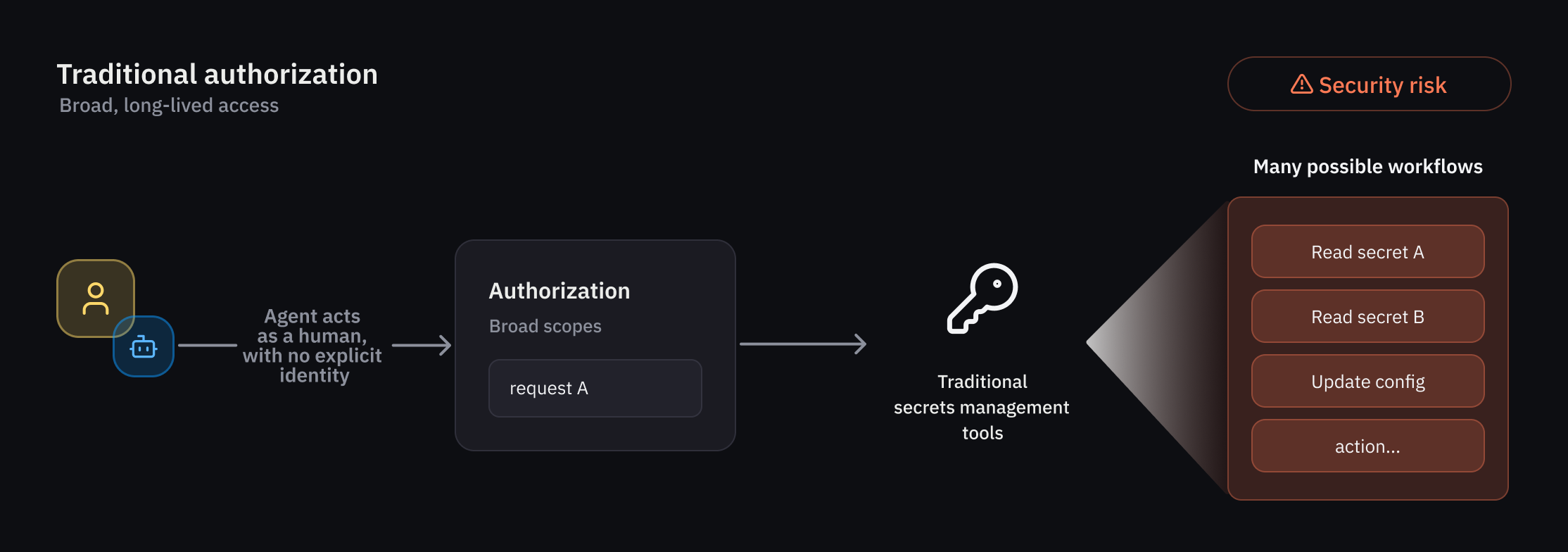
Traditional IAM was built for deterministic users and workflows—where identity, actions, and access scopes are known in advance. AI agents, however, are autonomous and non-deterministic; they may act unpredictably, rely on delegation, and require temporary, tightly scoped permissions. Vault addresses this by combining identity, delegation tracking, runtime policy evaluation, and ephemeral authorization. This model ensures that each agent action is authorized in real time, based on its identity, the human or system it represents, and the specific transaction context. Without such a model, organizations face risks of overprivileged agents, unaccountable actions, and security blind spots.
2. What key security challenges does Vault solve for AI agents?
AI agents introduce operational and security complexities that Vault specifically targets. First, agents often operate less predictably than humans or traditional non-human identities (NHIs), requiring guardrails that can be enforced dynamically. Second, agents need fine‑grained authorization evaluated at runtime, scoped to individual actions or workflows rather than static roles. Third, clear attribution and auditability are critical because agents act on behalf of users—delegation must be explicitly tracked. Finally, organizations need a standardized approach to secure agents across diverse environments (cloud, on‑prem, hybrid). Vault's new capabilities answer these challenges with an agent registry, identity‑based policies, and per‑request authorization.
3. What is the agent registry and how does it work?
The agent registry is a new primitive in Vault that allows developers to register and manage agent activity separately from humans and traditional NHIs. This separation is vital for delegation flows where an agent uses an on‑behalf‑of (OBO) pattern, carrying a human user's authority with consent. The registry ensures that every delegation is explicitly tracked, forming the foundation for a dedicated framework of registration, authorization, credential management, and observability. Administrators can view all registered agents, monitor their permissions, and revoke access when necessary. By isolating agent identities, Vault provides agent‑specific oversight that is essential for auditing and enforcing least privilege in AI workflows.
4. How does Vault enforce least privilege for non‑deterministic agents?
Vault applies deterministic guardrails and per‑request access control to govern agent behavior. Because agent actions can vary unpredictably, static policies are insufficient. Instead, Vault evaluates trust across multiple dimensions at runtime—considering the agent's identity, its delegated authority, the target system, and the specific action requested. Administrators define granular identity‑based policies that restrict agents to only the secrets and credentials needed for a given workflow. For example, a coding agent may access a database secret only for the duration of a deployment task. This runtime evaluation ensures that even if an agent behaves in unexpected ways, it cannot exceed the scope of its authorized actions.
5. How does delegation (on‑behalf‑of) and consent work for AI agents in Vault?
AI agents frequently operate in delegation mode, acting on behalf of a human user. Vault supports the on‑behalf‑of (OBO) pattern where the agent explicitly carries the user's identity and consent. The agent registry tracks this delegation link, ensuring that every action can be attributed to both the agent and the delegating user. When the agent requests access to a secret, Vault evaluates multiple trust dimensions: the agent's own identity, the user's permissions, and the consent granted for that specific workflow. This provides a clear audit trail and prevents privilege escalation. For example, a support agent can access a customer's data only when the customer has consented, and the access is automatically revoked after the task completes.
6. What is per‑request (ephemeral) authorization and why is it critical for agents?
Per‑request authorization grants temporary, tightly scoped access rights that expire after a specific task or timeframe. For AI agents, this is critical because they may process multiple requests concurrently and require just‑in‑time credentials. Instead of issuing long‑lived tokens, Vault issues a credential only for the duration of a single request or workflow. This reduces the risk of credential misuse if an agent is compromised or behaves incorrectly. Ephemeral authorization also simplifies credential management—agents obtain new credentials for each request, eliminating the need to store or rotate secrets. Administrators can define policies that limit the lifetime of such access to seconds or minutes, aligning with the agent's operational context.
7. When will these capabilities be generally available?
Select customers are currently evaluating these capabilities through an early access program. Broader public beta availability is planned for a future Vault release this summer. HashiCorp is actively incorporating feedback from early adopters to refine the agent registry, policies, and ephemeral authorization controls. Organizations interested in securing their AI agent deployments can join the early access program or plan to adopt the features when they enter public beta. The final GA release will include comprehensive documentation and integration guides for common agent frameworks.
Related Articles
- The Alaskan Mega-Tsunami That Almost Was: 7 Startling Facts About the Tracy Arm Landslide
- What the National Science Board Mass Firing Means for U.S. Science Policy
- Unveiling the Top Terminal Annoyances: Insights from 1,600 Users
- ACEMAGIC F5A AI 470: Ryzen AI HX 370 Powers This Compact Desktop
- Uber Unveils All-in-One Travel Platform, Challenges Expedia and Airbnb
- The Evolution of Attraction in Resident Evil: From Leon to Lady Dimitrescu
- The Hidden Cost of AI-Assisted Coding: Why Your Code Review Process Is Struggling
- Unlocking the Power of Blocks: A Universal Protocol for the Web